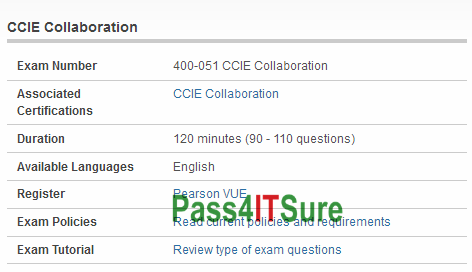
Is going for the brain dumps for Cisco 400-051 dumps the right way? The CCIE Collaboration (400-051 CCIE Collaboration) exam is a 120 minutes (90 – 110 questions) assessment in pass4itsure that is associated with the CCIE Collaboration certification. Guiding you towards success about 100% pass Cisco 400-051 dumps CCIE Collaboration pdf with a high score video study. “CCIE Collaboration” is the exam name of Pass4itsure Cisco 400-051 dumps test which designed to help candidates prepare for and pass the Cisco 400-051 exam. Cisco 400-051 exam practice test software that help the students with the help of https://www.pass4itsure.com/400-051.html dumps PDF format on the websites having all the information about these Cisco CCIE Collaboration Written, so that the students dont have to face any problems in Cisco 400-051 exam.
[2018 New Pass4itsure 400-051 Dumps Version From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWNkViTVpuUWl4SGs
[2018 New Pass4itsure 400-101 Dumps Version From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWczJDVzl1SUJLWms
To Get More Information About Cisco 400-051 Dumps Exam Go Here(6-18)
QUESTION 6
A Company security System Administrator is reviewing the network system log files. He notes the following: What should he assume has happened and what should he do about the situation?
A. He should contact the attacker’s ISP as soon as possible and have the connection disconnected.
B. He should log the event as suspicious activity, continue to investigate, and take further steps according to site security policy.
C. He should log the file size, and archive the information, because the router crashed.
D. He should run a file system check, because the Syslog server has a self correcting file system problem.
E. He should disconnect from the Internet discontinue any further unauthorized use, because an attack has taken place.
400-051 exam Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
You should never assume a host has been compromised without verification. Typically, disconnecting a server is an extreme measure and should only be done when it is confirmed there is a compromise or the server contains such sensitive data that the loss of service outweighs the risk. Never assume that any administrator or automatic process is making changes to a system. Always investigate the root cause of the change on the system and follow your organizations security policy.
QUESTION 7
To what does “message repudiation” refer to what concept in the realm of email security?
A. Message repudiation means a user can validate which mail server or servers a message was passed through.
B. Message repudiation means a user can claim damages for a mail message that damaged their reputation.
C. Message repudiation means a recipient can be sure that a message was sent from a particular person.
D. Message repudiation means a recipient can be sure that a message was sent from a certain host.
E. Message repudiation means a sender can claim they did not actually send a particular message.
Correct Answer: E
Explanation
Explanation/Reference:
Explanation:
A quality that prevents a third party from being able to prove that a communication between two other parties ever took place. This is a desirable quality if you do not want your communications to be traceable.
Non-repudiation is the opposite quality–a third party can prove that a communication between two other parties took place. Non-repudiation is desirable if you want to be able to trace your communications and prove that they occurred. Repudiation Denial of message submission or delivery.
QUESTION 8
How does Traceroute map the route that a packet travels from point A to point B?
A. It uses a TCP Timestamp packet that will elicit a time exceed in transit message.
B. It uses a protocol that will be rejected at the gateways on its way to its destination.
C. It manipulates the value of time to live (TTL) parameter packet to elicit a time exceeded in transit message.
D. It manipulated flags within packets to force gateways into generating error messages.
400-051 dumps Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
Traceroute works by increasing the “time-to-live” value of each successive batch of packets sent. The first three packets have a time-to-live (TTL) value of one (implying that they make a single hop). The next three packets have a TTL value of 2, and so on. When a packet passes through a host, normally the host decrements the TTL value by one, and forwards the packet to the next host. When a packet with a TTL of one reaches a host, the host discards the packet and sends an ICMP time exceeded (type 11) packet to the sender. The traceroute utility uses these returning packets to produce a list of hosts that the packets have traversed en route to the destination.
QUESTION 9
Snort has been used to capture packets on the network. On studying the packets, the penetration tester finds it to be abnormal. If you were the penetration tester, why would you find this abnormal? (Note: The student is being tested on concept learnt during passive OS fingerprinting, basic TCP/IP connection concepts and the ability to read packet signatures
from a sniff dumo.) 05/20-17:06:45.061034 192.160.13.4:31337 -> 172.16.1.101:1 TCP TTL:44 TOS:0x10 ID:242 ***FRP** Seq: 0XA1D95 Ack: 0x53 Win: 0x40005/20-17:06:58.685879 192.160.13.4:31337 -> 172.16.1.101:1024 TCP TTL:44 TOS:0x10 ID:242 ***FRP** Seg: 0XA1D95 Ack: 0x53 Win: 0x400 What is odd about this attack? (Choose the most appropriate statement)
A. This is not a spoofed packet as the IP stack has increasing numbers for the three flags.
B. This is back orifice activity as the scan comes from port 31337.
C. The attacker wants to avoid creating a sub-carrier connection that is not normally valid.
D. There packets were created by a tool; they were not created by a standard IP stack.
Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
Port 31337 is normally used by Back Orifice. Note that 31337 is hackers spelling of `elite’, meaning `elite hackers’.
QUESTION 10
Your company trainee Sandra asks you which are the four existing Regional Internet Registry (RIR’s)?
A. APNIC, PICNIC, ARIN, LACNIC
B. RIPE NCC, LACNIC, ARIN, APNIC
C. RIPE NCC, NANIC, ARIN, APNIC
D. RIPE NCC, ARIN, APNIC, LATNIC
400-051 pdf Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
All other answers include non existing organizations (PICNIC, NANIC, LATNIC). See
QUESTION 11
A very useful resource for passively gathering information about a target company is:
A. Host scanning
B. Whois search
C. Traceroute
D. Ping sweep
Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
A, C & D are “Active” scans, the question says: “Passively”
QUESTION 12
You receive an email with the following message: Hello Steve, We are having technical difficulty in restoring user database record after the recent blackout. Your account data is corrupted. Please logon to the SuperEmailServices.com and change your password. If you do not reset your password within 7 days, your account will be permanently disabled locking you out from our e-mail services. From this e-mail you suspect that this message was sent by some hacker since you have been using their e-mail services for the last 2 years and they have never sent out an e-mail such as this. You also observe the URL in the message and confirm your suspicion about 0xde.0xad.0xbde.0xef which looks like hexadecimal numbers. You immediately enter the following at Windows 2000 command prompt: Ping 0xde.0xad.0xbe.0xef You get a response with a valid IP address. What is the obstructed IP address in the e-mail URL?
A. 222.173.190.239
B. 233.34.45.64
C. 54.23.56.55
D. 199.223.23.45
400-051 vce Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
0x stands for hexadecimal and DE=222, AD=173, BE=190 and EF=239
QUESTION 13
Which of the following tools are used for footprinting?(Choose four.
A. Sam Spade
B. NSLookup
C. Traceroute
D. Neotrace
E. Cheops
Correct Answer: ABCD
Explanation
Explanation/Reference:
Explanation:
All of the tools listed are used for footprinting except Cheops.
QUESTION 14
According to the CEH methodology, what is the next step to be performed after footprinting?
A. Enumeration
B. Scanning
C. System Hacking
D. Social Engineering
E. Expanding Influence
400-051 exam Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
Once footprinting has been completed, scanning should be attempted next. Scanning should take place on two distinct levels: network and host.
QUESTION 15
NSLookup is a good tool to use to gain additional information about a target network. What does the following command accomplish?
nslookup
> server <ipaddress>
> set type =any
> ls -d <target.com>
A. Enables DNS spoofing
B. Loads bogus entries into the DNS table
C. Verifies zone security
D. Performs a zone transfer
E. Resets the DNS cache
Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
If DNS has not been properly secured, the command sequence displayed above will perform a zone transfer.
QUESTION 16
While footprinting a network, what port/service should you look for to attempt a zone transfer?
A. 53 UDP
B. 53 TCP
C. 25 UDP
D. 25 TCP
E. 161 UDP
F. 22 TCP
G. 60 TCP
400-051 dumps Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
IF TCP port 53 is detected, the opportunity to attempt a zone transfer is there.
QUESTION 17
Your lab partner is trying to find out more information about a competitors web site. The site has a .com extension. She has decided to use some online whois tools and look in one of the regional Internet registrys. Which one would you suggest she looks in first?
A. LACNIC
B. ARIN
C. APNIC
D. RIPE
E. AfriNIC
Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
Regional registries maintain records from the areas from which they govern. ARIN is responsible for domains served within North and South America and therefore, would be a good starting point for a .com domain.
QUESTION 18
Network Administrator Patricia is doing an audit of the network. Below are some of her findings concerning DNS. Which of these would be a cause for alarm? Select the best answer.
A. There are two external DNS Servers for Internet domains. Both are AD integrated.
B. All external DNS is done by an ISP.
C. Internal AD Integrated DNS servers are using private DNS names that are
D. unregistered.
E. Private IP addresses are used on the internal network and are registered with the internal AD integrated DNS server.
400-051 pdf Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
A. There are two external DNS Servers for Internet domains. Both are AD integrated. This is the correct answer. Having an AD integrated DNS external server is a serious cause for alarm. There is no need for this and it causes vulnerability on the network.
B. All external DNS is done by an ISP. This is not the correct answer. This would not be a cause for alarm. This would actually reduce the company’s network risk as it is offloaded onto the ISP. C. Internal AD Integrated DNS servers are using private DNS names that are unregistered. This is not the correct answer. This would not be a cause for alarm. This would actually reduce the company’s network risk.
D. Private IP addresses are used on the internal network and are registered with the internal AD integrated DNS server. This is not the correct answer. This would not be a cause for alarm. This would actually reduce the company’s network risk.
See What Our Customers Are Saying:
We at Pass4itsure are committed to our customer’s success. There are 50,000+ customers who used this preparation material for the preparation of various certification exams and this number of customers is enough for new candidates to trust in these products.Our Cisco 400-051 dumps are created with utmost care and professionalism. We utilize the experience and knowledge of a team of industry professionals from leading organizations all over the world.
Cisco 400-051 exam braindumps PDF, are basically the 400-051 dumps exam questions as well as the answers that are taken from Cisco CCIE Collaboration Written exam.”CCIE Collaboration”, also known as 400-051 exam, is a Cisco certification which covers all the knowledge points of the real Cisco exam. Pass4itsure Cisco 400-051 dumps exam questions answers are updated (615 Q&As) are verified by experts. The associated certifications of https://www.pass4itsure.com/400-051.html dumps is CCIE Collaboration.
Read More Youtube: https://youtu.be/B4_e531hZRg

Compared with other brands, Pass4itsure has up to dated exam information, affordable price, instant exam PDF files downloaded, error correction, unlimited install,etc. Such as Pass4itsure Cisco 400-051 Dumps PDF, Download Cisco 400-051 Dumps PDF With A High Score, We Help You Pass CCIE Collaboration. Simple and Easy! To take advantage of the guarantee, simply contact Customer Support, requesting the exam you would like to claim. Pass4itsure guarantee insures your success otherwise get your MONEYBACK!